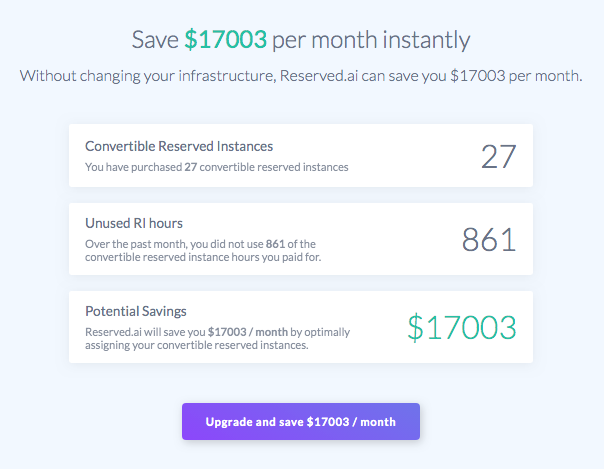
Reserved.ai
Reserved.ai is a platform that automates purchasing, renewing and exchanging your AWS Reserved Instances: Optimizing cloud savings so you can focus on Building
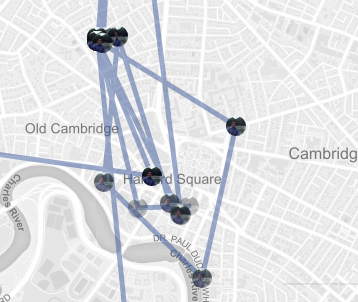
A now defunct Chrome Browser Extension that aggregated and displayed location data shared by your friends via Facebook Messenger.
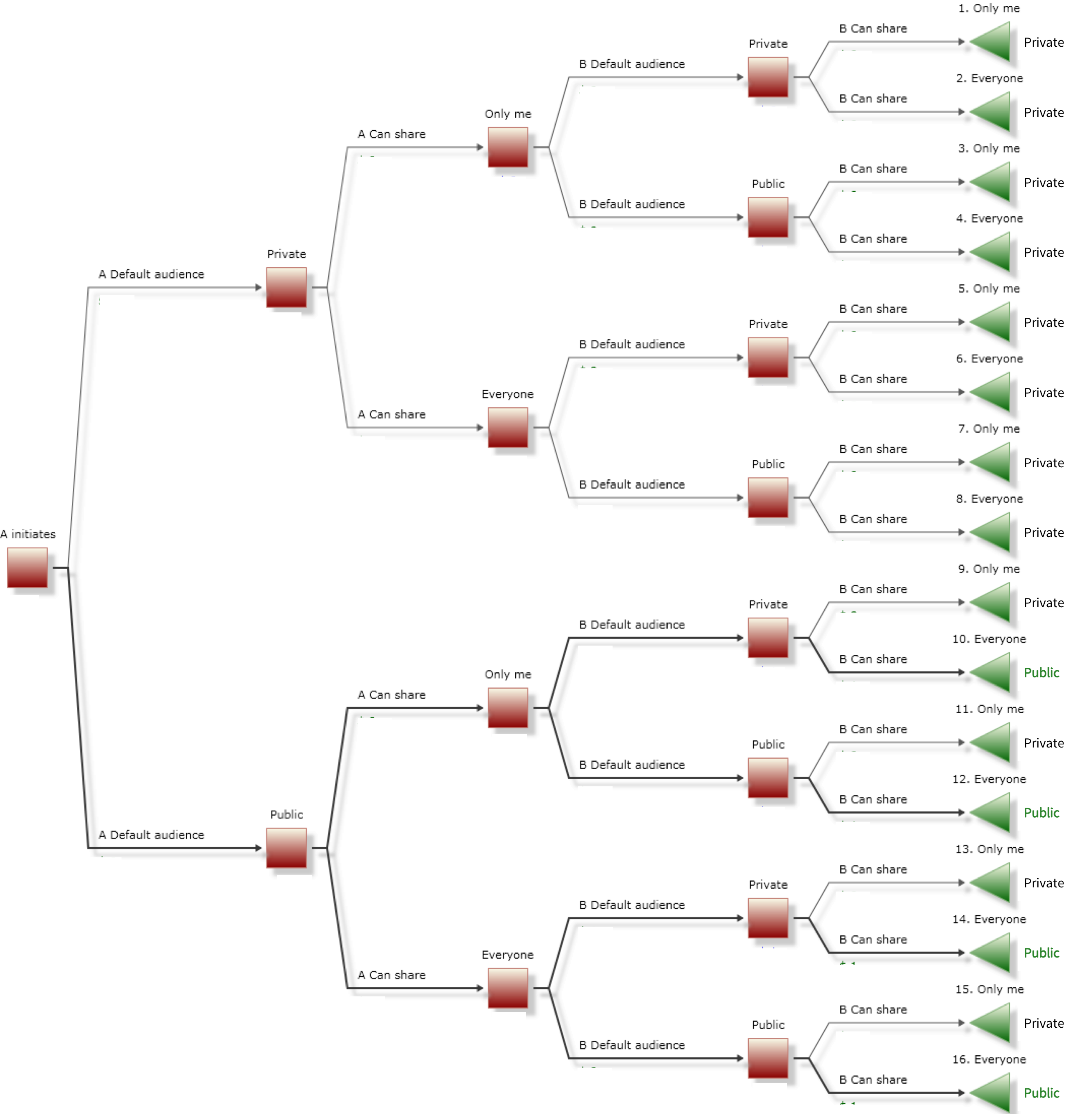
A paper edited by Latanya Sweeney published in Harvard's Technology Science Journal highlighting how Venmo's default privacy settings cause users to inadvertantly publicly share a large amount of private data.
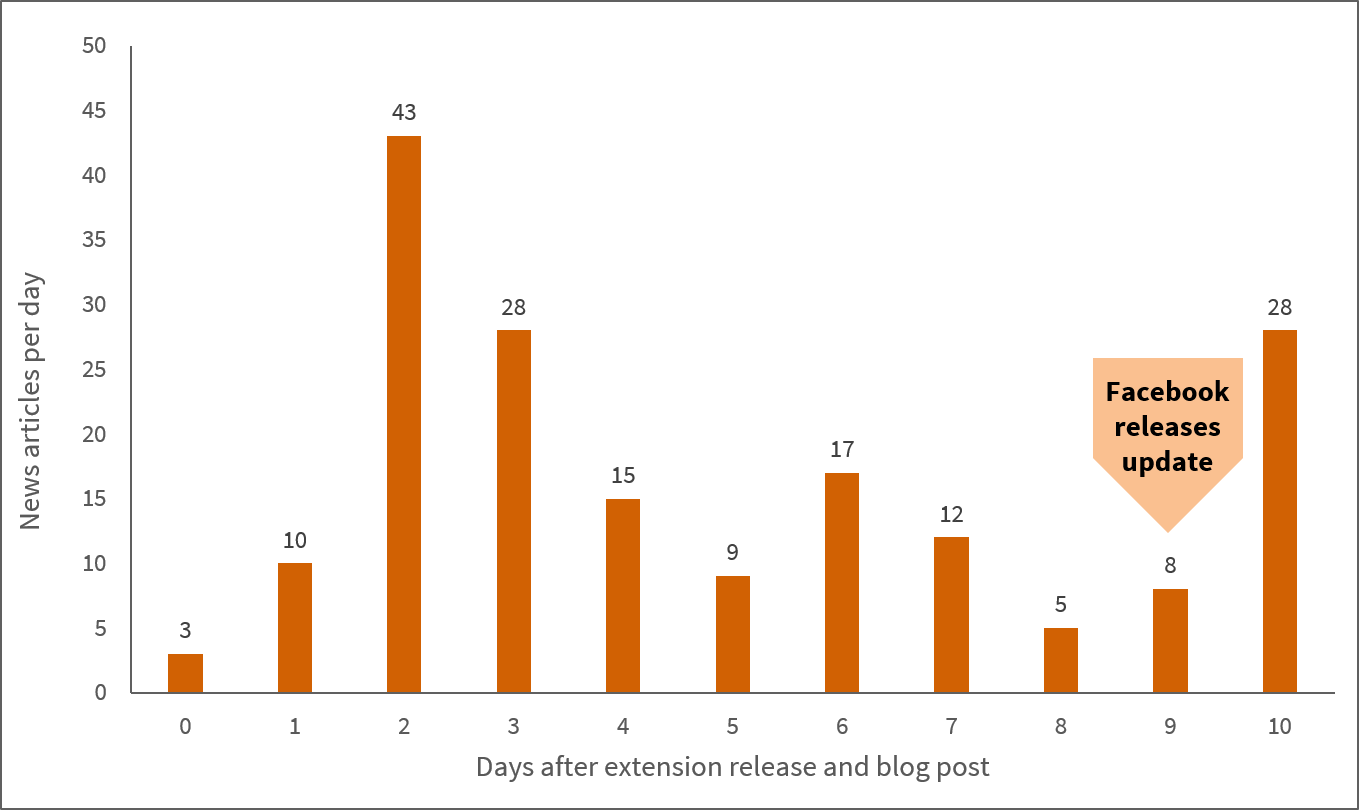
A paper edited by Latanya Sweeney published in the inaugural issue of Harvard's Technology Science Journal highlighting issues with Facebook's response to a privacy incident. Covered by Boston.com, Forbes, The Washington Post and over 400 other global publications.